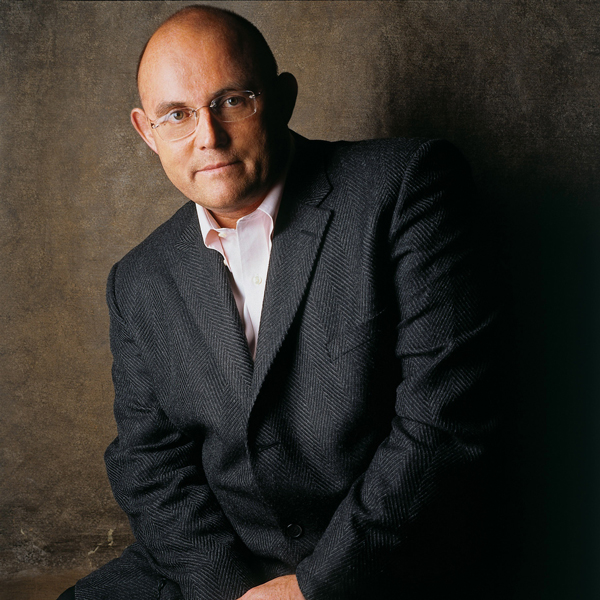
Morgan Wright
- On the Front Lines: Street Crime to Cybercrime
- Cybersecurity Expert
- Interviewer and Moderator
In Person-Fee 🛈
$5,000 - $10,000
Virtual Fee:
$7,500 and Under
Travels From
District of Columbia
Morgan Wright Speaker Biography
Morgan Wright is an internationally recognized expert on cybersecurity strategy, cyberterrorism, identity theft, and privacy. His landmark testimony before Congress on Healthcare.gov changed how the government collected personally identifiable information. He has made hundreds of appearances on national news, radio, print, and web, and has spoken to audiences around the world. Previously Morgan was a Senior Advisor in the US State Department Antiterrorism Assistance Program and Senior Law Enforcement Advisor for the 2012 Republican National Convention. In addition to 18 years in state and local law enforcement, Morgan has developed solutions in defense, justice, and intelligence for the largest technology companies in the world.
A highly seasoned interviewer and moderator, Morgan has helped the largest companies in the world shape and change markets through effective, engaging interviews with senior executives and newsmakers in the complex world of cybersecurity and cyberterrorism. Whether it’s moderating a product launch panel discussion with the world's most famous hacker, or interviewing the CIO of the world's largest security company, Morgan delivers with compelling questions and insight honed by 30 years of expertise. This includes over 400 appearances on national news shows where he's been interviewed as well by the best in the business. Discussion and interview goals are always to inspire, inform and entertain with just the right amount of humor and wit.
To book Morgan Wright contact Executive Speakers Bureau @ 901-754-9404
Cyberstrike: Warfare in the Fifth Domain
A coordinated cyber strike is launched against Ukraine during the coldest winter on record, taking out large numbers of power plants and crippling water systems. At the same time, the Russian Federation launches a massive cyber attack, taking out the power grid in several countries and disrupting communications and water systems. Massive civil unrest taxes first responders beyond the breaking point and requires military assistance from NATO forces internationally. The culmination of a two-year espionage operation by the GRU, the military intelligence arm of the Russian Federation, double agents occupy key critical infrastructure positions in Ukraine. The Russian Federation seizes the country without a shot. How did this happen? A printer cartridge and falsified work histories.
In this keynote, Morgan walks you through how warfare will be fought in the future, the role of cybersecurity, the importance of properly vetting employees for key positions and why traditional network security is failing to protect us.
Healthcare is Big Business: Why Capitalism Has Made Healthcare The #1 Target for Hackers and Organized Crime
There is a reason healthcare has overtaken the retail industry as the #1 target for hackers and organized crime. And that reason is capitalism. Medical records on the internet black market can fetch 140 times as much as a credit card number. With the increase in ransomware attacks, hospitals and healthcare facilities are directly in the crosshairs of opportunistic hackers and criminals. These adversaries are better armed, better trained and better equipped to attack than healthcare is to defend. But there is hope. Fighting back takes lessons from the Spartan Warriors and why their shield was so important. Morgan shows healthcare organizations how to understand and respond to the current threats, what’s coming next, and how to take a few simple steps that will raise the shields of your organization.
Hackers and Scammers and Thieves! Oh my!
Hackers, scammers and thieves have one mission - to separate you from your money and identity. With so much focus on staying safe online, criminals are successfully targeting you with ever-evolving techniques and tactics that don't involve your smartphone or computer. Learn how to stay safe online, offline and in the real world. Learn from real examples of how criminals are coming after you.
Small Business is Big Business to Hackers
Three out of five cyber attacks target small to medium-sized businesses. The myth of hackers only going after large companies is thoroughly debunked in this eye-opening presentation. Morgan clearly spells out ‘why’ hackers like smaller companies, and what these companies need to do before its too late.
The Growing Threat of Social Media and Terrorism
“Strike the soldiers…strike their police, security and intelligence members…” was the message is a video posted by ISIS on a hacked US Central Command (CENTCOM) YouTube channel. That was after hacking CENTCOM’s twitter account as well - a hack that could have been prevented with a remarkably simple tool. The growing use of propaganda spread by social media is inspiring terrorism here and abroad. From San Bernardino to Paris, terrorists are using advanced technology and social media in ways that frustrate the ability of law enforcement to monitor and prevent future attacks. This provocative presentation looks at how we’re losing the war of influence and what can be done about it.
Hacking The Human: You Are The Weakest Link
In this fascinating presentation, Morgan draws upon his skills with behavioral analysis interviewing and shows how hackers and terrorists are going after the weakest link in any organization - you. From social engineering to spear phishing, the largest attacks and data breaches have occurred because of human weakness. From his time instructing damage assessment agents at the highly secretive NSA (agents who investigated the biggest espionage cases of all time) to the FBI, state and local law enforcement, Morgan shows how this same human weakness can actually be used to defend against new threats.
End Of Days: The Threat of Terrorism To Critical Infrastructure
“If you want to hit a country severely you hit its power and water supplies. Cyber technology can do this without shooting a single bullet.” So said Major General Isaac Ben-Israel of the Israeli Air Force. The US critical infrastructure is highly at risk from a coordinated cyber attack against key elements of our power grid. The BlackEnergy malware attack in Ukraine on Dec. 23, 2015, that left 800,000 homes without power, was the first verified cyberattack against an electrical grid. This same malware has thoroughly infected our own systems, leaving the United States in grave danger from an extensive, and extended cyberattack. What should be done from a policy and technology perspective is the takeaway from this timely presentation.
Moderator, Discussion Leader & Interviewer
A highly seasoned interviewer and moderator, Morgan has helped the largest companies in the world shape and change markets through effective, engaging interviews with senior executives and newsmakers in the complex world of cybersecurity and cyberterrorism. Whether it’s moderating a product launch panel discussion with the world’s most famous hacker, or interviewing the CIO of the world’s largest security company, Morgan Wright delivers with compelling questions and insight honed by 30 years of expertise. This includes over 400 appearances on national news shows where’s he’s been interviewed as well by the best in the business. Discussions and interviews goals are always to inspire, inform and entertain with just the right amount of humor and wit.






















October 29, 2021
Morgan is passionate and enthusiastic about his work. Lot of real time examples were covered by him and very practical tips were provided. He was whole heartedly involved during the exchange of question and answers at the end of the session.
HQ, NV Bekaert SA Helpful 0